In today’s interconnected world, organizations face the constant challenge of safeguarding their digital assets while ensuring smooth operations. This is where Identity and Access Management (IAM) comes into play. IAM is a critical framework that allows organizations to manage user identities, control access to resources, and protect against potential security risks. In this blog post, we will delve into the significance of IAM, its key components, benefits, and best practices, enabling you to establish a robust security foundation.
The Importance of Identity and Access Management:
In a rapidly evolving digital landscape fraught with cyber threats, IAM plays a vital role in ensuring the security of organizational data. Here’s why IAM is essential:
Enhanced Security:
IAM acts as a shield, protecting organizations against unauthorized access and potential data breaches. By implementing strong authentication methods, authorization protocols, and centralized user management, IAM ensures that only authorized individuals gain access to critical resources.
Regulatory Compliance:
In today’s regulatory environment, organizations must comply with various data privacy and security regulations, such as GDPR, HIPAA, or PCI DSS. IAM solutions provide the necessary controls and auditing capabilities to meet these compliance requirements, minimizing the risk of penalties and reputational damage.
Improved Operational Efficiency:
IAM streamlines user provisioning and deprovisioning processes, ensuring that employees have the appropriate access privileges at the right time. This eliminates the administrative burden of manual access management, enhances productivity, and reduces errors.
User Experience:
IAM solutions offer a seamless user experience through features like Single Sign-On (SSO). With SSO, users can access multiple applications and resources using a single set of credentials, eliminating the need to remember multiple passwords and enhancing convenience.
Centralized Identity Management:
IAM provides a centralized repository for managing user identities, permissions, and attributes. This simplifies administration, reduces the risk of identity duplication, and allows for efficient user lifecycle management.
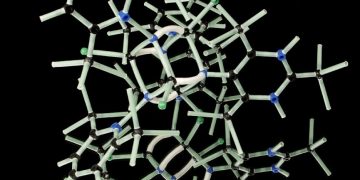
Key Components of Identity and Access Management:
IAM comprises several key components that work together to create a comprehensive security framework:
Identity Governance and Administration (IGA):
IGA focuses on managing user identities, roles, and entitlements. It includes activities such as user provisioning, access request management, and role-based access control (RBAC).
Authentication and Authorization:
Authentication verifies the identity of users, ensuring they are who they claim to be. Authorization determines the level of access and permissions granted to authenticated users based on their roles and responsibilities.
Single Sign-On (SSO):
SSO enables users to access multiple applications and systems using a single set of login credentials. It simplifies the login process and improves user experience.
Privileged Access Management (PAM):
PAM focuses on securing privileged accounts with elevated access privileges. It includes password management, session monitoring, and secure remote access to privileged systems.
Identity Federation:
Identity federation allows secure sharing of identities between different organizations or systems, enabling users from one organization to access resources in another organization without the need for separate user accounts.
To ensure successful implementation of IAM within your organization, consider the following best practices:
Develop a Comprehensive IAM Strategy:
Define clear goals, objectives, and a roadmap for implementing IAM. Assess your organization’s current security risks, identify key stakeholders, and establish policies and procedures.
Enforce Strong Authentication Mechanisms:
Implement multi-factor authentication (MFA) to add an extra layer of security. MFA combines multiple factors such as passwords, biometrics, and security tokens to verify user identities.
Implement Least Privilege:
Grant users the minimum access rights necessary to perform their job functions. Regularly review and update user permissions to align with current roles and responsibilities.
Regularly Monitor and Audit Access:
Implement continuous monitoring and auditing of user access and activities. This helps detect and respond to unauthorized or suspicious activities promptly.
Educate and Train Users:
Promote cybersecurity awareness among employees and provide training on IAM best practices, such as password hygiene, recognizing phishing attempts, and reporting suspicious activities.
In an era of increasing cyber threats, Identity and Access Management (IAM) is crucial for organizations to safeguard their digital assets effectively. By implementing an IAM strategy, organizations can enhance security, ensure regulatory compliance, improve operational efficiency, and provide a seamless user experience. Remember to consider the key components of IAM, such as identity governance, authentication, SSO, privileged access management, and identity federation, while following best practices for successful implementation.
Remember, implementing IAM is an ongoing process that requires continuous monitoring, regular updates, and user education. By prioritizing IAM and staying vigilant, organizations can establish a strong security foundation and protect their digital kingdom.