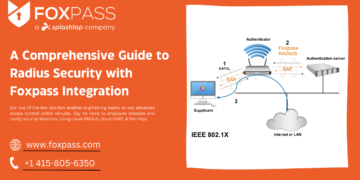
Introduction:
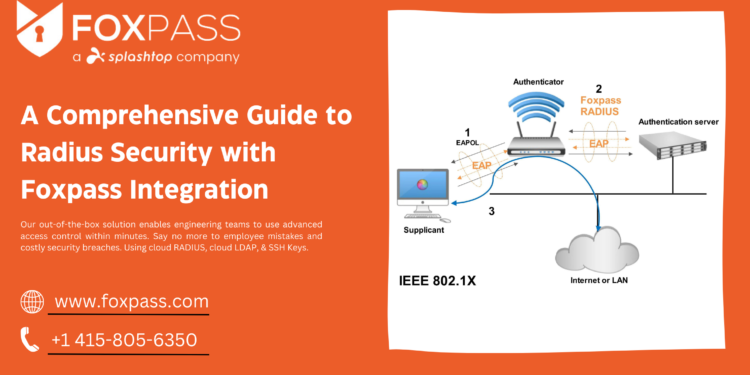
In an increasingly interconnected world, where network security threats are ever-present, organizations must adopt robust measures to protect their sensitive data and resources. One powerful approach to bolstering network security is the integration of Radius authentication and Foxpass, a versatile identity and access management solution. This comprehensive guide aims to provide a detailed understanding of Radius security and the seamless integration of Foxpass, equipping organizations with the knowledge to enhance their network security effectively.
1. Introduction to Radius Authentication:
Radius, short for Remote Authentication Dial-In User Service, is a widely adopted networking protocol that enables centralized authentication and authorization for remote network access. It operates based on a client-server model, where a Radius client (typically a network access server) forwards authentication requests to a Radius server for verification. The server authenticates user credentials against a central user database, providing secure access control to the network.
2. Key Benefits of Radius Authentication:
Radius authentication offers several key benefits that contribute to robust network security. These include:
– Strong User Authentication: By validating user credentials against a central database, Radius ensures that only authorized individuals can access the network, reducing the risk of unauthorized access.
– Centralized Access Control: With Radius, organizations can enforce consistent access control policies across their network infrastructure, providing a centralized mechanism to manage user privileges and permissions.
– Scalability and Flexibility: Radius is highly scalable and can accommodate diverse network infrastructures, making it suitable for organizations of all sizes. It supports various authentication methods, including passwords, digital certificates, and two-factor authentication (2FA), allowing organizations to choose the level of security that fits their needs.
3. Introduction to Foxpass:
Foxpass is a cloud-based identity and access management platform that integrates with existing directory services, such as Microsoft Active Directory and LDAP. It provides a comprehensive suite of tools for user management, access control and security enhancements.
4. Advantages of Foxpass Integration with Radius:
Integrating Foxpass with Radius authentication brings several advantages to the table:
– Simplified User Management: Foxpass simplifies the administration of user accounts, group memberships, and access policies. Organizations can leverage their existing directory services and seamlessly synchronize user information, ensuring efficient user management across the network.
– Granular Access Control: Foxpass enables organizations to define and enforce granular access control policies. Administrators can assign users to specific groups, define resource access rules, and manage permissions centrally, reducing the risk of unauthorized access.
– Two-Factor Authentication (2FA): Foxpass supports 2FA, providing an extra layer of security to the authentication process. Users can utilize methods such as TOTP, SMS verification, or push notifications to authenticate themselves, significantly reducing the risk of compromised accounts due to weak or stolen passwords.
– Audit and Compliance: The integration of Foxpass with Radius authentication facilitates comprehensive audit trails and logging capabilities. Organizations can track user access, monitor authentication events, and generate detailed reports to comply with regulatory requirements and identify potential security breaches.
5. Implementation and Best Practices:
Implementing Radius security with Foxpass integration involves configuring the Radius client, establishing a connection with the Radius server, and integrating Foxpass to synchronize user information and access policies. It is essential to follow best practices such as regularly updating passwords, enabling strong authentication methods, and conducting regular security audits to maintain an optimal security posture.
6. Real-World Use Cases and Success Stories:
Highlighting real-world use cases and success stories can provide insights into how organizations have leveraged Radius security with Foxpass integration to enhance their network security measures. These examples can demonstrate the effectiveness and benefits of the integration in different industries and scenarios.
In conclusion: the integration of Radius authentication and Foxpass offers organizations a powerful solution to enhance network security. By leveraging centralized authentication, granular access control, two-factor authentication, and comprehensive audit capabilities, organizations can establish.